The 2025 Guide to NERC CIP-014 Physical Security Mandates
NERC CIP-014 is the North American Electric Reliability Corporation standard that requires transmission station owners and operators to evaluate the physical security risks of their critical facilities and develop plans to mitigate those risks. With enforcement actions increasing and audit scrutiny tightening, understanding the specific requirements of R5 and R6 has never been more important for utility security teams.
This guide breaks down the standard requirement by requirement, explains what auditors are actually looking for, and provides a practical compliance checklist you can use to prepare for your next assessment. Whether you are a utility security director, a compliance officer, or a security integrator working with electric utilities, this is the reference you need.
What Is NERC CIP-014?
NERC CIP-014 was developed in response to the 2013 Metcalf sniper attack on a Pacific Gas and Electric substation in California. That incident, in which attackers disabled 17 transformers with rifle fire, exposed a critical vulnerability in the nation's grid infrastructure: most substations had little to no physical security beyond chain-link fencing and basic signage.
The standard applies to transmission stations and substations that meet specific criticality thresholds based on their impact on the Bulk Electric System (BES). It requires owners to perform risk assessments (R1), have those assessments verified by a third party (R2), develop and implement physical security plans (R4/R5), and have those plans reviewed by an independent entity (R6).
Requirement R5: The Physical Security Plan
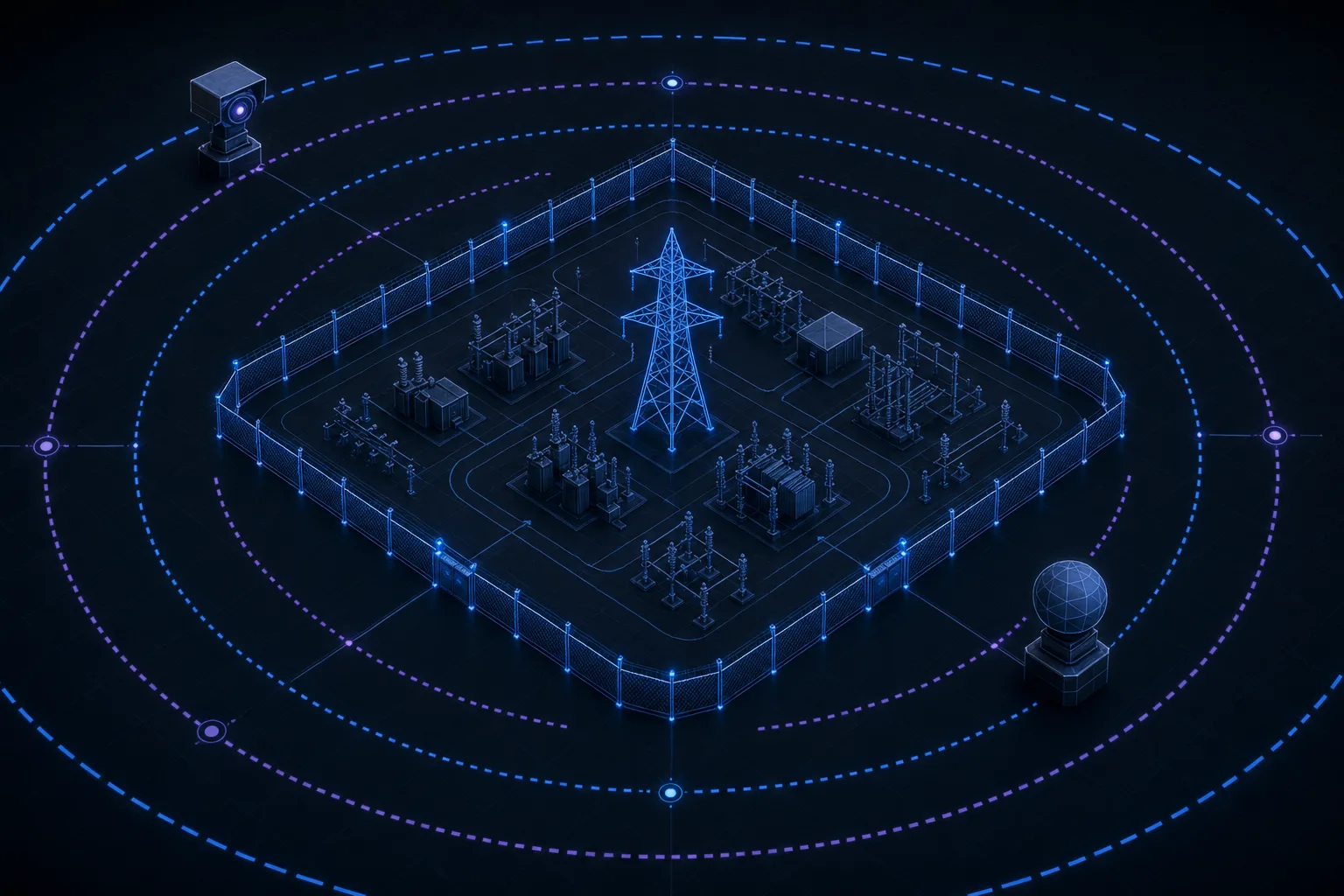
R5 is the core of CIP-014. It mandates that each applicable transmission station must have a documented physical security plan that addresses the threats identified in the risk assessment. The plan must include specific measures to deter, detect, delay, assess, communicate, and respond to potential physical threats.
- Deter: Visible security measures such as fencing, lighting, signage, and the presence of surveillance cameras that discourage potential attackers from attempting an intrusion.
- Detect: Technologies and processes that identify a physical security breach as it occurs. This includes perimeter intrusion detection systems (PIDS), video analytics with motion detection, radar, and thermal imaging.
- Delay: Physical barriers that slow an attacker's progress, buying time for response forces to arrive. Hardened fencing, anti-climb measures, vehicle bollards, and ballistic-rated enclosures all fall into this category.
- Assess: The ability to evaluate an alarm or alert and determine whether it represents a genuine threat. This typically requires high-resolution cameras with PTZ capability and trained monitoring personnel.
- Communicate: Established protocols for notifying law enforcement, grid operators, and internal stakeholders when a physical security event occurs.
- Respond: Documented response procedures including law enforcement coordination, mutual aid agreements, and escalation criteria for different threat levels.
Key Insight
Auditors are not just looking for equipment on site. They want to see documented evidence that each layer of your security plan has been tested, that personnel have been trained on response procedures, and that the plan is reviewed and updated at least annually.
Requirement R6: Third-Party Plan Review
R6 requires that the physical security plan developed under R5 be reviewed by an unaffiliated third party with relevant security expertise. This reviewer must have no financial or organizational conflict of interest with the transmission owner. The review must evaluate whether the plan adequately addresses the threats identified in the risk assessment and whether the proposed security measures are appropriate and sufficient.
The third-party reviewer must provide written findings, and the transmission owner must document how each finding was addressed. If a recommendation is not implemented, the owner must provide a documented justification for why it was not adopted. This creates a paper trail that auditors will examine closely.
Perimeter Monitoring Technologies That Meet the Standard
The standard does not prescribe specific technologies, which gives utilities flexibility but also creates uncertainty about what auditors expect. Based on our experience working with utilities across the country, the following technologies consistently satisfy the detect and assess requirements:
Recommended Detection Technologies
| Technology | Detection Range | False Alarm Rate | Best For |
|---|---|---|---|
| Fence-Mounted Sensors | Perimeter contact | Medium | Cut/climb detection |
| Ground-Based Radar | Up to 500m | Low | Open terrain, large perimeters |
| Thermal Cameras | Up to 2km | Low | Night detection, all weather |
| Video Analytics (AI) | Camera FOV dependent | Low | Human classification |
| Buried Fiber Optic | Perimeter contact | Very Low | Covert detection zones |
Preparing for a CIP-014 Audit
NERC audits for CIP-014 are thorough and documentation-heavy. Auditors typically spend two to three days on site and request extensive evidence packages in advance. The most common findings that lead to violations involve incomplete documentation rather than inadequate security measures. In other words, you might have excellent physical security but still fail the audit if you cannot prove it on paper.
Here are the areas where utilities most frequently receive findings:
- Missing evidence of plan review. R6 requires a third-party review every 36 months. If you cannot produce the review report and your documented response to each finding, that is a violation.
- Incomplete threat assessment updates. If your risk assessment references threats from three years ago without evidence of annual review, auditors will flag it.
- No testing records for detection systems. If you have perimeter sensors and cameras but cannot show maintenance logs and periodic detection tests, the auditor cannot verify the system works.
- Gaps in response coordination. Your plan must include documented coordination with local law enforcement. Auditors may verify this with the responding agency.
CIP-014 Compliance Checklist
Use this checklist to evaluate your current compliance posture before your next audit cycle:
- Risk assessment completed and identifies all applicable transmission stations (R1)
- Third-party verification of risk assessment on file (R2)
- Physical security plan documents deter, detect, delay, assess, communicate, and respond measures (R5)
- Detection systems installed and operational at all applicable stations
- Quarterly testing records for all perimeter detection and surveillance systems
- Law enforcement coordination agreements documented and current
- Response procedures documented with escalation criteria
- Personnel training records for security plan and response procedures
- Third-party plan review completed within the last 36 months (R6)
- Documented responses to all third-party review findings
Conclusion
NERC CIP-014 compliance is not a one-time project. It is an ongoing program that requires continuous monitoring, regular testing, annual plan reviews, and periodic third-party assessments. The utilities that pass audits consistently are the ones that treat physical security as an operational discipline rather than a checkbox exercise.
At Zimy Electronics, we have designed and deployed CIP-014 compliant perimeter security systems for transmission owners across the country. Our engineering team understands both the technical requirements and the documentation expectations that auditors look for. If you are preparing for an upcoming audit or upgrading your substation security program, we can help you build a system that satisfies the standard and actually protects your assets.