Integrating Legacy SCADA with Modern VMS
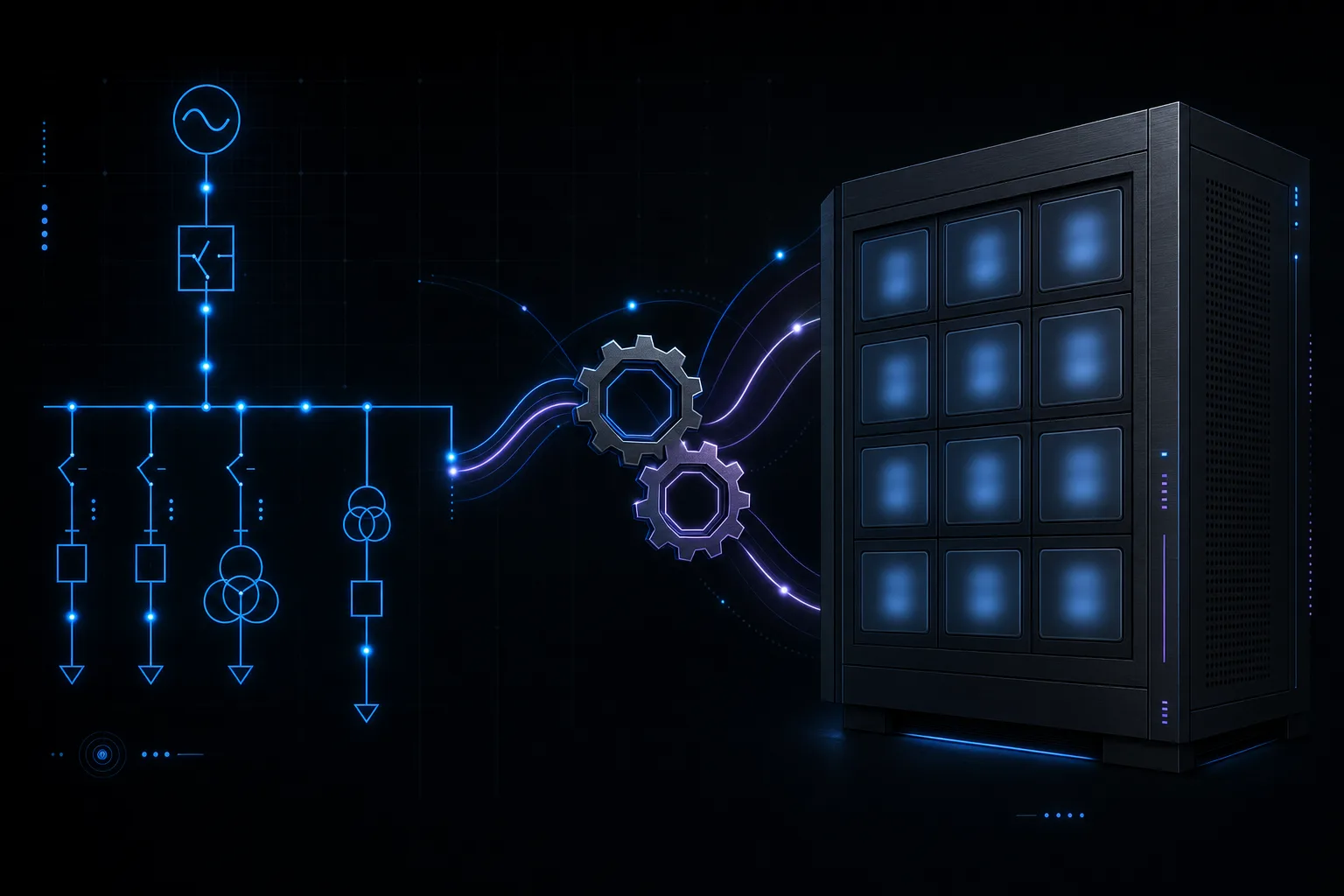
Most electric utilities operate two completely separate technology stacks for their substations. The Operational Technology (OT) side runs SCADA systems that monitor and control electrical equipment: breakers, reclosers, transformers, and capacitor banks. The Information Technology (IT) side runs physical security systems: cameras, access control, and intrusion detection. These two worlds have historically been managed by different teams, run on different networks, and use different protocols.
But the convergence of OT and IT is no longer optional. NERC CIP standards increasingly require correlation between physical security events and cyber security events. Insurance carriers want unified incident timelines. And operationally, it makes no sense to have a SCADA operator see a transformer fault alarm but not know that someone broke through the perimeter fence five minutes earlier. This article provides practical strategies for bridging legacy SCADA systems with modern Video Management Systems (VMS) without ripping out expensive infrastructure.
The Convergence Challenge
The fundamental challenge is that SCADA and VMS speak different languages, operate on different timescales, and were designed with different security models. SCADA systems communicate using industrial protocols like DNP3, Modbus, and IEC 61850. VMS platforms use IP-based protocols like ONVIF, RTSP, and proprietary APIs. Getting these systems to share data requires a translation layer that respects the security boundaries of both environments.
There is also an organizational challenge. OT engineers are protective of their SCADA networks for good reason: a misconfigured device on the OT network could potentially cause a grid disturbance. IT security teams are equally protective of their domain. Any integration project must navigate both technical and political boundaries.
Critical Rule
Never connect a VMS or any IT system directly to the OT/SCADA network. All data exchange must pass through a properly configured demilitarized zone (DMZ) with firewalls, data diodes, or protocol break points. Violating this principle creates cyber security vulnerabilities that could have grid-level consequences.
Architecture Patterns for Integration
There are three common architectural approaches to SCADA-VMS integration, each with different tradeoffs in complexity, cost, and security posture:
Pattern 1: One-Way Data Push via OPC-UA
In this pattern, the SCADA system publishes alarm and status data to an OPC-UA server in the DMZ. The VMS subscribes to relevant data points and uses them to trigger camera presets, initiate recording, or display contextual overlays. Data flows in one direction only: from SCADA to VMS. The VMS never sends commands back to SCADA.
This is the most common and lowest-risk approach. OPC-UA supports built-in encryption and authentication, and the one-way data flow ensures that a compromised VMS cannot affect SCADA operations. Most modern SCADA platforms (OSIsoft PI, GE iFIX, Schneider ClearSCADA) support OPC-UA natively.
Pattern 2: Modbus TCP Alarm Mapping
For legacy SCADA systems that do not support OPC-UA, Modbus TCP provides a simpler alternative. Security alarm states (perimeter breach, door forced, motion detected) are mapped to Modbus registers in the SCADA database. When a register value changes, the SCADA HMI displays the corresponding alarm. This approach is less elegant than OPC-UA but works with virtually any SCADA system manufactured in the last 30 years.
The integration typically requires a protocol gateway device that sits in the DMZ and translates between the VMS alarm output (usually a REST API or SNMP trap) and Modbus TCP registers that the SCADA RTU can poll. These gateways cost $500 to $2,000 per unit and can handle hundreds of alarm points.
Pattern 3: Unified Platform with API Middleware
The most sophisticated approach uses API middleware to create a unified event stream from both SCADA and VMS. Platforms like Genetec Security Center and Milestone XProtect offer SCADA integration plugins that can ingest SCADA alarms and display them alongside video events in a single operator interface. This gives operators a true "single pane of glass" view where they can see a transformer overtemperature alarm, the associated thermal camera feed, and the access control log for that substation all in one display.
This pattern requires the most engineering effort and the closest collaboration between OT and IT teams, but it delivers the highest operational value. It is the preferred approach for utilities building new control centers or upgrading existing ones.
Protocol Bridging in Practice
Regardless of which architecture pattern you choose, the actual data exchange requires mapping between two fundamentally different data models. SCADA thinks in terms of points, registers, and analog/digital values. VMS thinks in terms of events, alarms, and camera streams. Here is how common security events map across the boundary:
Event Mapping: Security to SCADA
| Security Event | SCADA Representation | Operator Action |
|---|---|---|
| Perimeter breach (Zone 1) | Digital Input DI-101 = 1 | View live camera, dispatch |
| Door forced open | Digital Input DI-102 = 1 | Verify via camera, log event |
| Access granted (valid card) | Digital Input DI-103 = pulse | Log for compliance (CIP-006) |
| Camera offline | Digital Input DI-104 = 1 | Dispatch maintenance |
| Thermal alarm (equipment) | Analog Input AI-201 = temp | Cross-reference with SCADA temps |
Network Segmentation Best Practices
The network architecture for a SCADA-VMS integration must enforce strict segmentation between the OT network, the security network, and the corporate IT network. The following principles should guide your design:
- Dedicated DMZ for integration. All data exchange between SCADA and VMS passes through a hardened DMZ with firewalls on both sides. No direct connections between OT and IT networks.
- Data diodes for high-security sites. For critical substations, consider hardware-enforced one-way data flow using optical data diodes. These physically prevent any data from flowing back into the OT network.
- Separate VLANs for camera traffic. Video streams should be on their own VLAN, isolated from both the OT network and general corporate traffic. This prevents bandwidth contention and limits the blast radius of a compromise.
- Encrypted tunnels for remote access. If operators need to view camera feeds from a centralized control room, use encrypted VPN tunnels or ZTNA (Zero Trust Network Access) rather than extending the flat network.
Key Insight
The goal of SCADA-VMS integration is correlation, not control. You want operators to see security events alongside operational data so they can make better decisions faster. You do not want or need the VMS to send commands to SCADA equipment. Keep the data flow unidirectional wherever possible.
Conclusion
Integrating legacy SCADA with modern VMS is not a rip-and-replace project. It is a carefully planned convergence that preserves the integrity and security of both systems while creating a unified operational picture. The right architecture pattern depends on your SCADA platform, your VMS, your network infrastructure, and your organizational readiness.
At Zimy Electronics, we have executed SCADA-VMS integrations for utilities running platforms ranging from decades-old Modbus RTU systems to modern IEC 61850 environments. Our engineering team works closely with both OT and IT stakeholders to design integrations that are secure, reliable, and operationally valuable. If you are exploring convergence for your utility, we can help you choose the right approach and execute it safely.